Bluetooth - Get Cyber Safe
If hackers can detect your Bluetooth, they can get access to your device. Learn how to take care when using Bluetooth devices like speakers and headphones.

How to protect yourself from a Bluetooth cyber attack

Bluetooth Attacks and How to Secure Your Mobile Device from Vulnerabilities

The biggest risks of using Bluetooth trackers like Apple AirTag, Tile

Cybersecurity 101: Everything on how to protect your privacy and stay safe online

Cyber Security Threats in the Auto Industry and How to Prevent Them

How to remain Cyber-Safe

Bluetooth security: is Bluetooth safe from hackers? - Atlas VPN

Bluetooth Low Energy (BLE) Security and Privacy for IoT
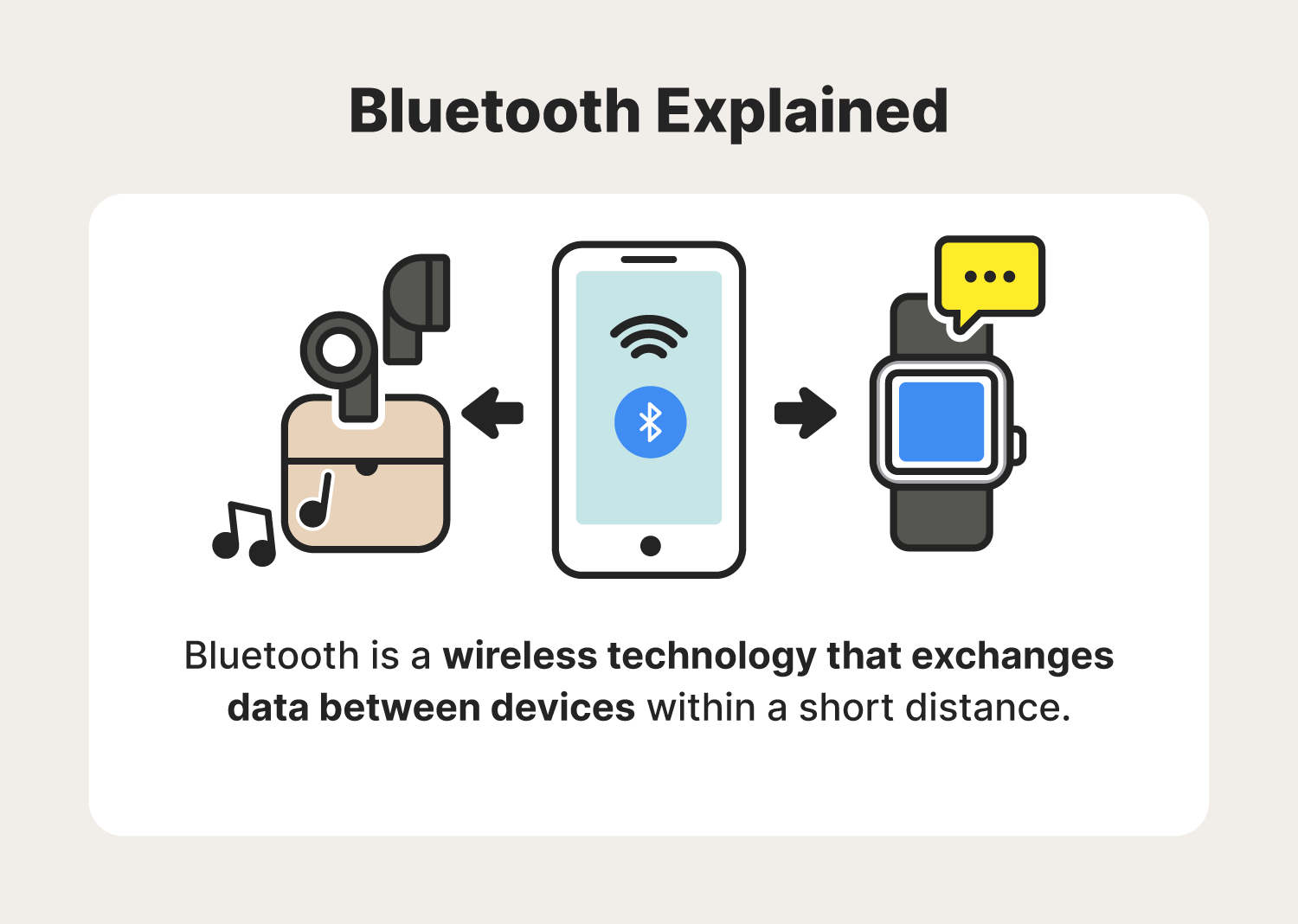
Bluetooth security risks to know + how to avoid them - Norton
USB Powered Speaker with Bluetooth – Connection to PC, Mac or Chromebook with a single USB cable and simultaneously connect to your smartphone with

Cyber Acoustics USB & Bluetooth Speaker Bar (CA-2890BT) – USB Powered Speaker with Speakerphone for PC and Bluetooth to Simultaneously Connect to
Bluetooth Attacks and How to Secure Your Mobile Device from Vulnerabilities

Defend Against Wi-Fi Pineapple Attacks

The Top 24 Security Predictions for 2024 (Part 2)