Buffer overflow - Wikipedia
Anatomy of a Buffer Overflow Attack - Speaker Deck
Buffer overflow - Wikipedia
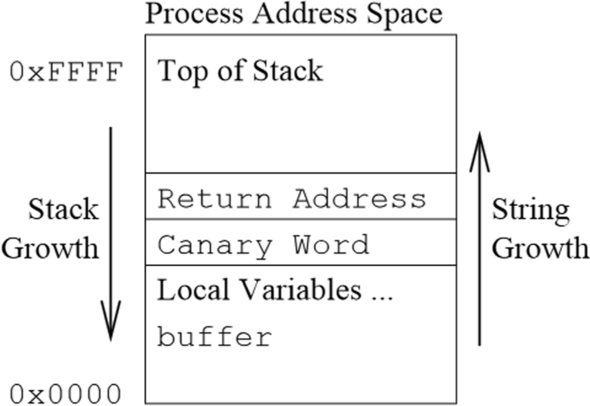
A buffer overflow detection and defense method based on RISC-V instruction set extension, Cybersecurity
What is Buffer Overflow? — TryHackMe: Buffer Overflow Prep Walkthrough, by caesar
Buffer Overflow: Introduction :: hg8's Notes — My notes about infosec world. Pentest/Bug Bounty/CTF Writeups.

Stack-based Memory Allocation: Stack, LIFO, Dynamic Memory Allocation, Stack Overflow, Automatic Variable, Application Binary Interface, PowerPC, MIPS Stack Buffer Overflow, Stack Machine - Surhone, Lambert M., Timpledon, Miriam T., Marseken, Susan
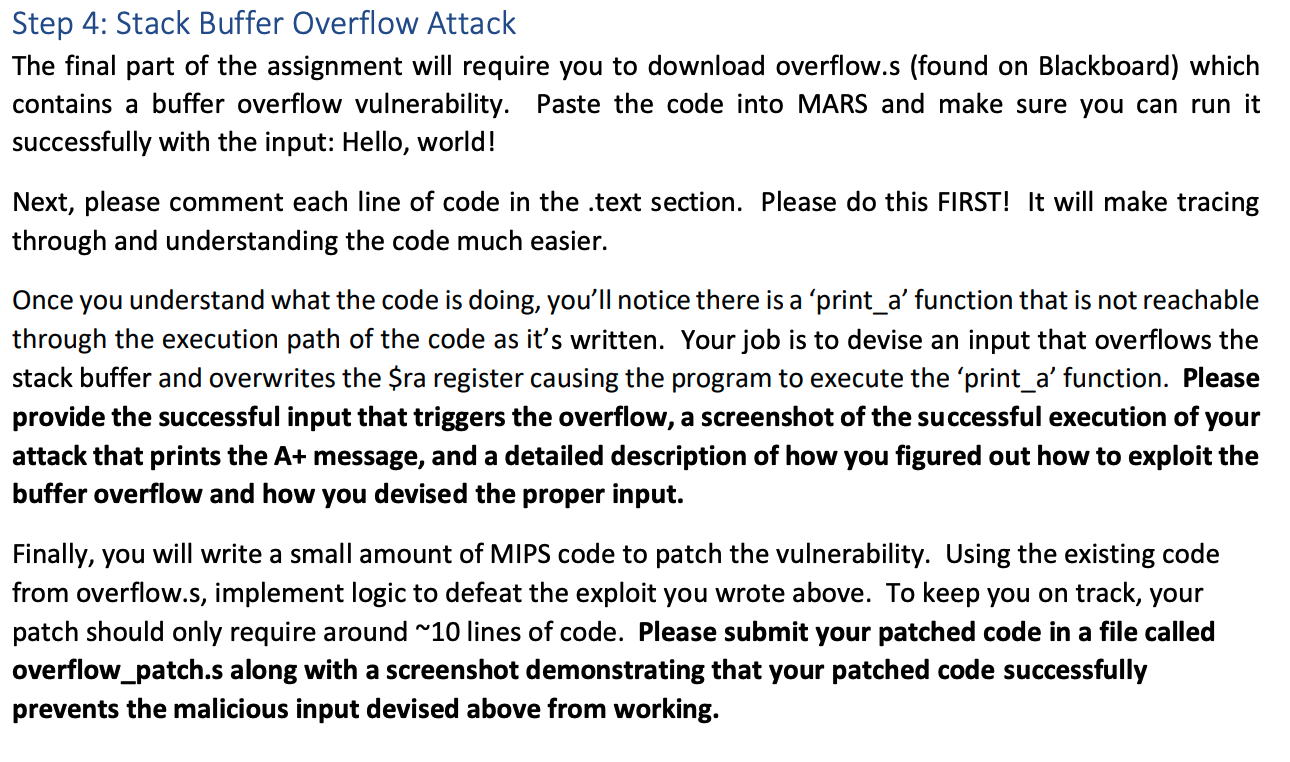
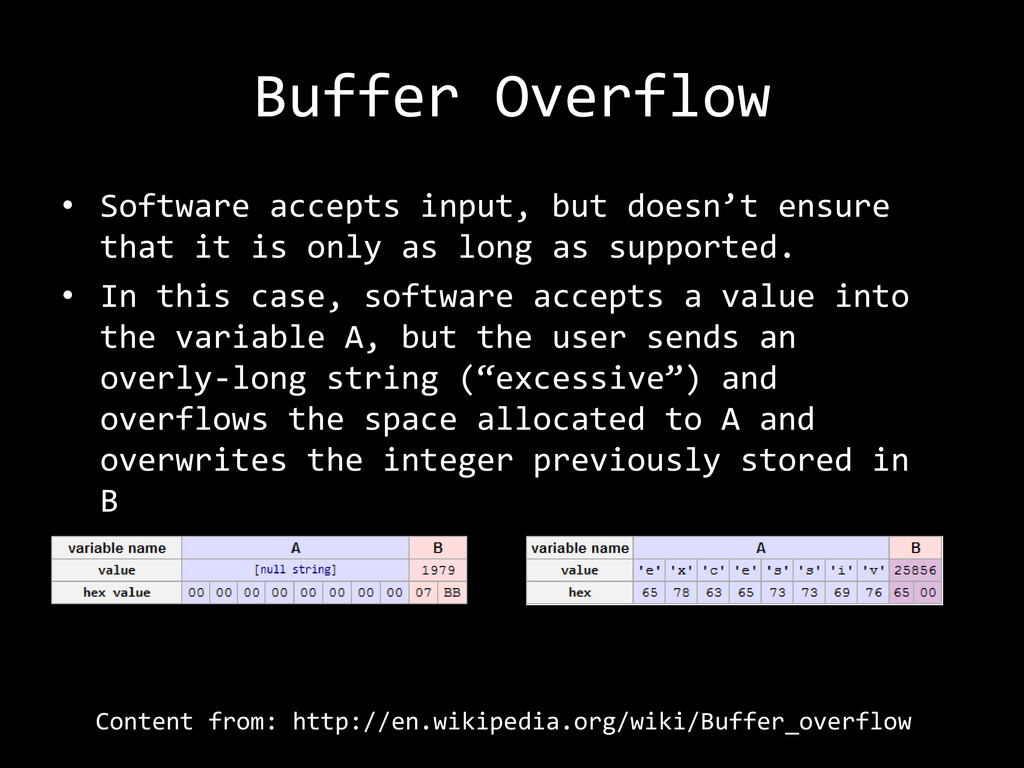
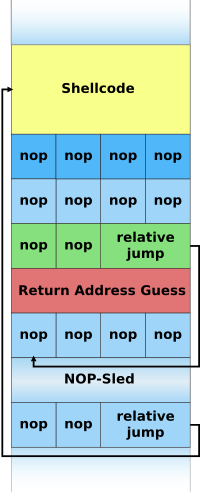
Introduction A stack buffer overflow attack occurs

Stack buffer overflow - Wikipedia

Information Security CS 526: Topic 9, PDF, Pointer (Computer Programming)
What is a buffer overflow? - Quora

A buffer overflow detection and defense method based on RISC-V instruction set extension, Cybersecurity