What is a Buffer Overflow Attack Types and Prevention Methods


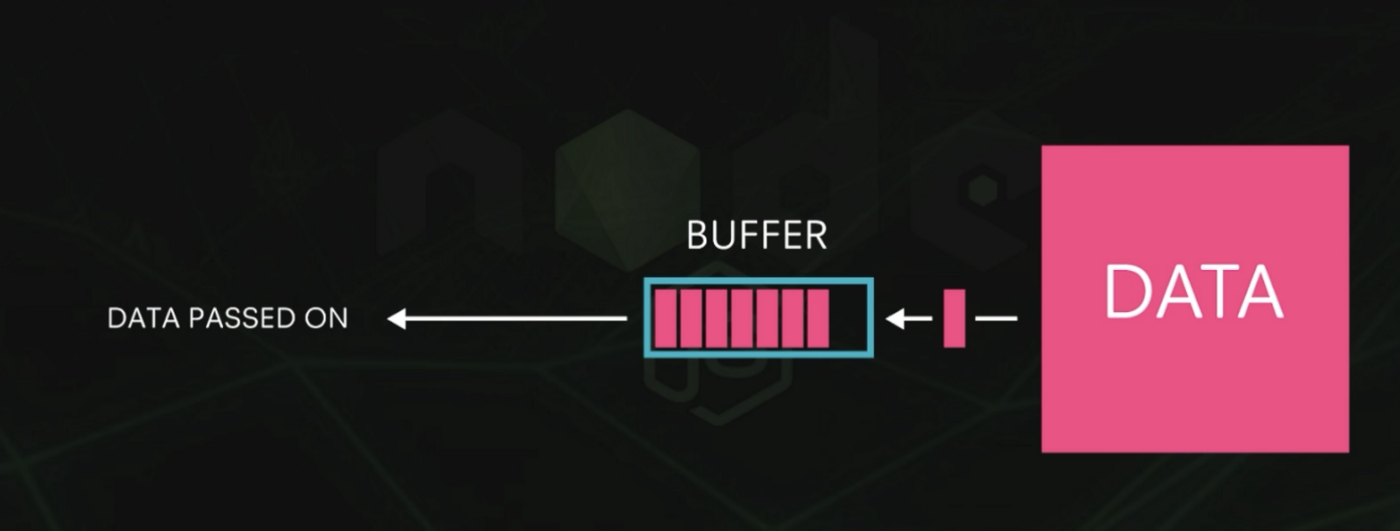
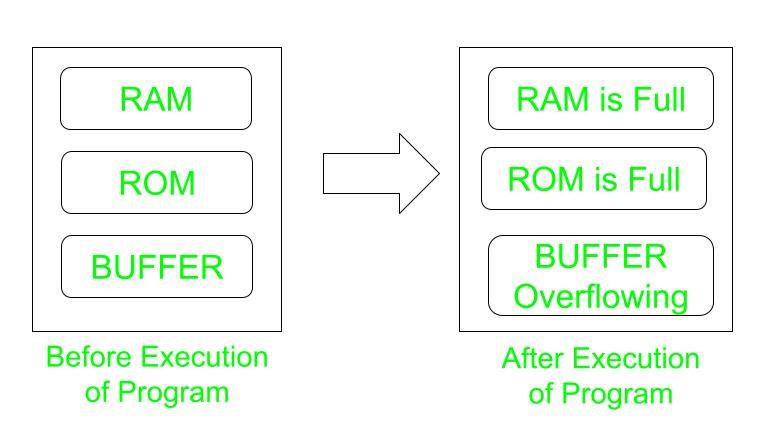
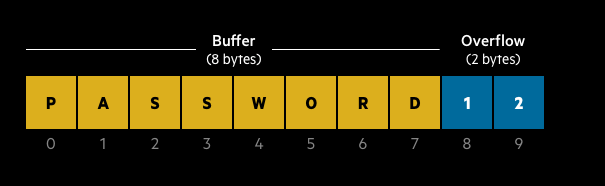
Buffer Overflow Attack Meaning, Types, and Prevention
Avoiding Buffer Overflows and Underflows
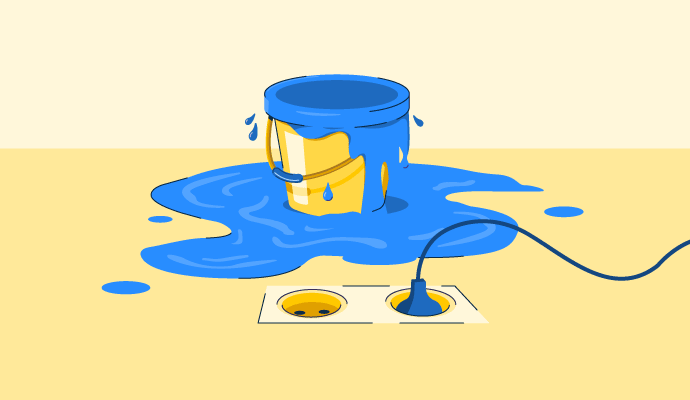
What is Buffer Overflow? Prevention and Types of Buffer Attacks
Identify, mitigate & prevent buffer overflow attacks on your systems

Exploit Development, Part 1: Anatomy of Buffer Overflows
Control Hijacking - GeeksforGeeks
Buffer Overflow Attack. A buffer overflow attack is a cyber…, by Ajay Yadav

ROP and Buffer Overflow: A Deadly Duo in Cybersecurity Exploits - FasterCapital
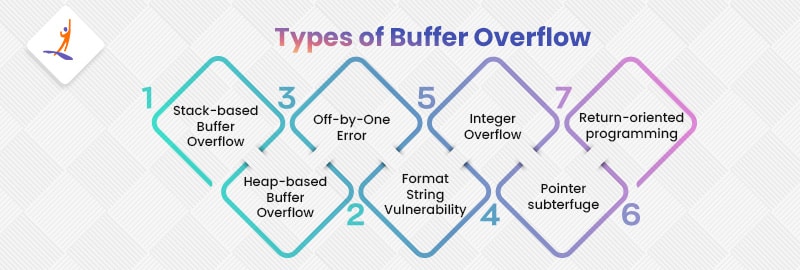
Buffer Overflow in Cyber Security - What is, Types, & Consequences
Sie können auch mögen



:max_bytes(150000):strip_icc():focal(749x0:751x2)/selena-gomez-music-health-summit-092023-1-21711c0248ec4cdbb4c047e54909dfe5.jpg)


:max_bytes(150000):strip_icc()/buffer-layer_final-bcc976c9c7e04aebb0c2dbd0dc4d606e.png)